Top 10 Crypto Bots: Automating Your Path to Prosperity
Discover the cream of the crypto trading bot , revolutionizing investment strategies with unmatched efficiency, accuracy, and potential for impressive returns.

The Complete Guide to Litecoin and the Benefits of Investing in It
Are you looking for a way to take your trading profits to the next level? Trading cryptocurrencies is one of the quickest ways to accomplish that goal; however, not all tokens are created equal. That’s why it pays—literally—to do your due diligence and pick out the coins with the best potential for growth according to Litecoin price prediction 2023. One digital asset traders need to consider: Litecoin (LTC). Aiming higher than simply being an “altcoin alternative”, Litecoin boasts impressive scalability and fast transactions capabilities which have made it one of today's most interesting investment opportunities in crypto. In this comprehensive guide, we'll introduce you to everything there is know about Litecoin, why so many investors already recognize its significant value – and just how much more it can offer as part of any crypto portfolio in 2023.

Bitcoin Margin Trading: Comparison of the 4 best margin brokers for day traders
Bitcoin trading has recently become very popular. Due to the high volatility, which is sometimes responsible for double-digit % losses/profits, day and swing traders can make enormous profits. While some do Bitcoin spot trading, i.e. simply buying/selling an asset, there...
BitMEX adds perpetual fiat currency contracts
Cryptocurrency exchange BitMEX has launched FX contracts – open-ended FX contracts with up to 50x leverage. It was announced on the platform’s official blog. FX contracts are traded around the clock. On weekends, the contract price fluctuates around Friday’s closing...
Binance subpoenaed over Ilon Musk’s refusal to buy Twitter
Twitter has subpoenaed a division of cryptocurrency exchange Binance over its allocation of funding for a takeover of the social network by Ilon Musk. This was reported by Bloomberg. In May, the trading platform provided the businessman with $500 million...
Sam Bankman-Fried backs bill to hand the CFTC oversight of the crypto market
FTX CEO Sam Bankman-Fried has praised a bill introduced in the US Congress to give the Futures Trading Commission (CFTC) the authority to regulate the cryptocurrency market. Bankman-Fried noted that the bill complements previous initiatives by Cynthia Lummis and Kirsten...
Poloniex to support potential PoW forks of Ethereum
Cryptocurrency exchange Poloniex will support a potential Proof-of-Work (PoW) fork of Ethereum after the merger of the core network with Beacon Chain, scheduled for September 2022. 📢 The Ethereum Merge is expected to be in September 2022. Poloniex was the...
Solana links massive hack to wallet provider Slope
The Solana team’s investigation into the hacking of thousands of cryptocurrency wallets found that the affected addresses were “at some point created, imported or used in Slope’s mobile apps”. Solana developers had previously reported that the hack was not caused...
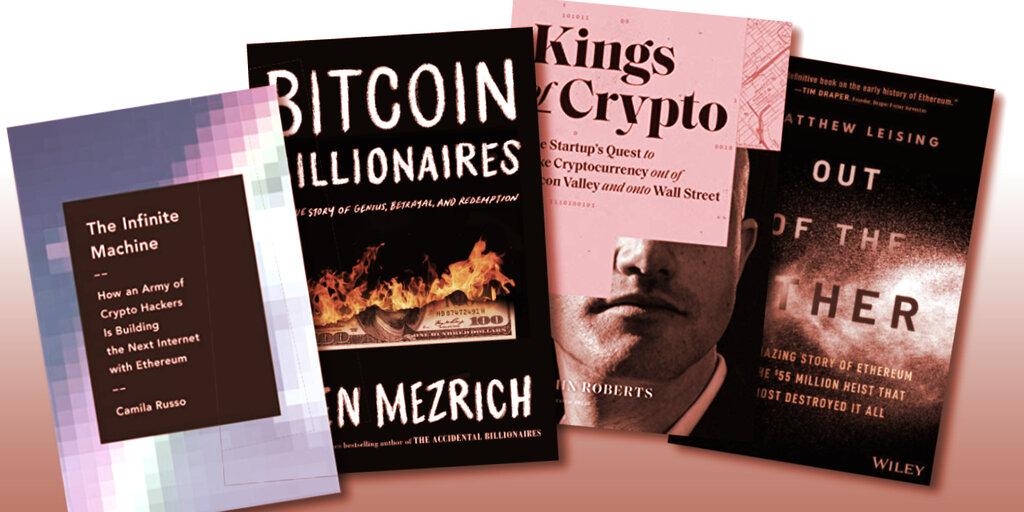
The Top 5 Bitcoin & Crypto Books
We present the best crypto books to satisfy your thirst for knowledge and enthusiasm. All books have already been read by us and recorded in an independent ranking of the Top 5 Bitcoin & Crypto Books 2022. Due to the...
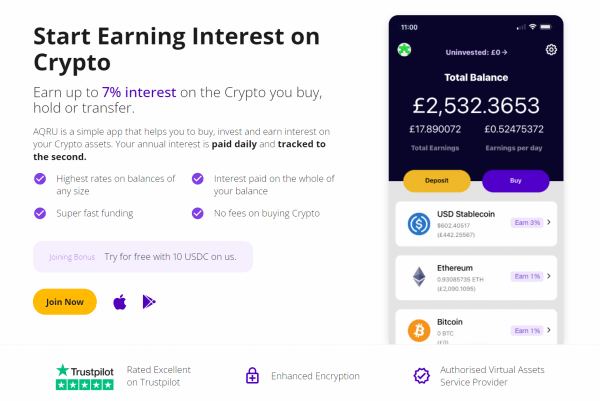
7 mobile apps for buying cryptocurrencies
It is no longer possible to imagine everyday life without the smartphone. Appointments, emails and even online banking are an integral part of every smartphone. Surely it must also be possible to buy cryptocurrencies via an app? It is! In...

